Trezor Login: The Ultimate Guide to Secure Wallet Access
Discover everything you need to know about Trezor Login — how it works, why it’s secure, and how to protect your crypto assets with confidence in 2025.
🔐
What Is Trezor Login?
Trezor Login is the secure authentication process that allows users to access their Trezor hardware wallet. Unlike traditional password systems, it requires physical interaction with your Trezor device — ensuring that only the owner can approve logins or transactions. This innovative security model has made Trezor one of the most trusted names in crypto storage, giving investors total control over their private keys and digital assets.
Quick Summary:
- Trezor Login uses hardware-based verification.
- No credentials or private keys ever leave your device.
- Compatible with Trezor Suite and third-party wallets.
- Ensures maximum protection from phishing and malware attacks.
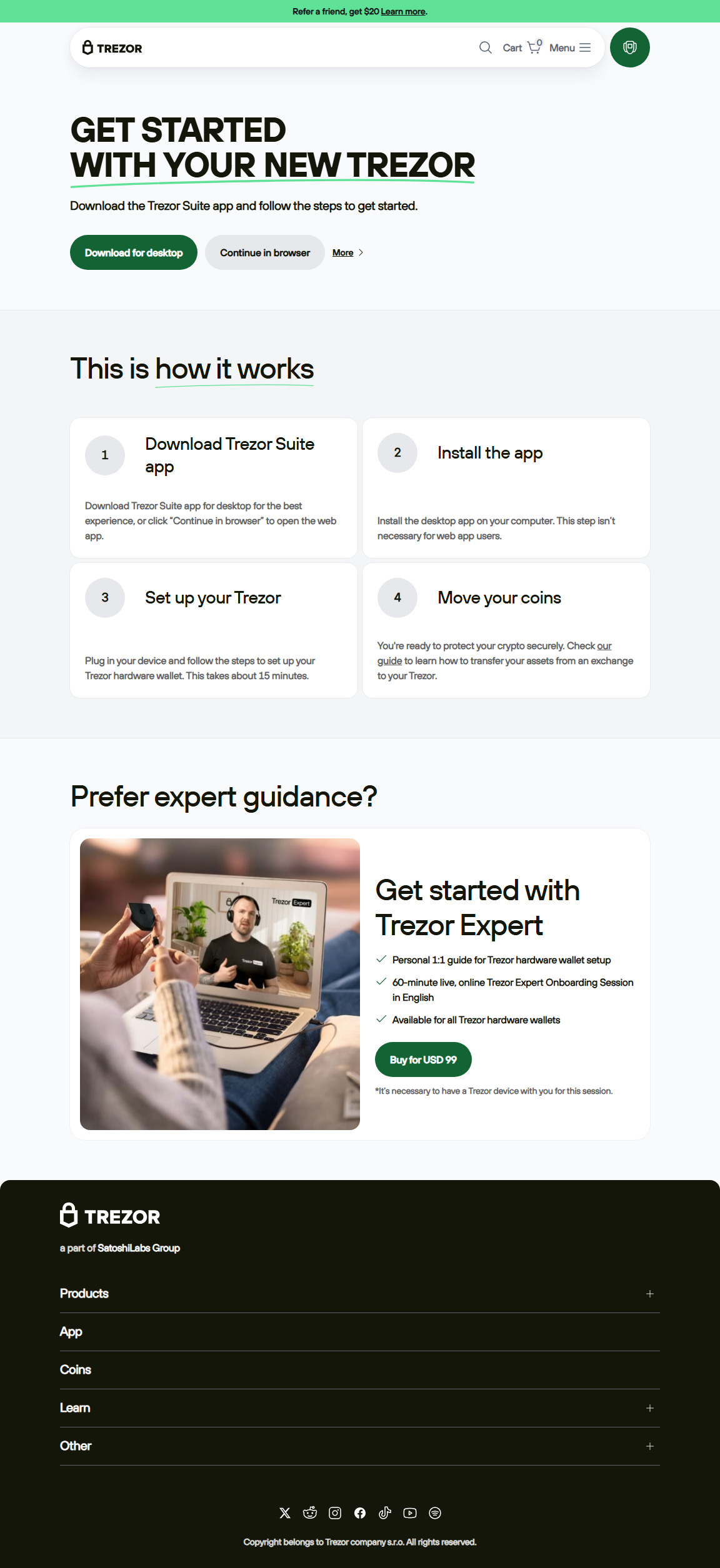
How to Log In to Your Trezor Wallet: Step-by-Step
Step 1: Connect Your Trezor Device
Use the official USB cable and connect your Trezor to your computer. Wait until your device lights up and displays the startup message.
Use the official USB cable and connect your Trezor to your computer. Wait until your device lights up and displays the startup message.
Step 2: Open Trezor Suite
Launch the Trezor Suite app — available for Windows, macOS, and Linux. The app will automatically detect your device and prompt you to log in.
Launch the Trezor Suite app — available for Windows, macOS, and Linux. The app will automatically detect your device and prompt you to log in.
Step 3: Enter Your PIN
Trezor uses a randomized PIN pad that appears differently each time. Match the numbers shown on your device to enter your PIN on the app interface.
Trezor uses a randomized PIN pad that appears differently each time. Match the numbers shown on your device to enter your PIN on the app interface.
Step 4: Confirm Login on Your Device
The device will show “Allow login?” Verify that it says “Trezor.io” or your official suite domain, then confirm directly on the Trezor device.
The device will show “Allow login?” Verify that it says “Trezor.io” or your official suite domain, then confirm directly on the Trezor device.
Step 5: Access Your Wallet Dashboard
Once approved, your wallet interface will unlock. You can now check balances, manage accounts, or sign transactions with confidence.
Once approved, your wallet interface will unlock. You can now check balances, manage accounts, or sign transactions with confidence.
💡 Analogy: Think of Trezor Login as a Bank Vault
The vault (Trezor device) holds your keys. Even if someone knows where the vault is, they can’t open it without the correct combination (your PIN and passphrase). Each login is a confirmation that you, and only you, have the authority to access your digital fortune.
Trezor Login vs. Other Crypto Wallets
| Feature | Trezor Login | Software Wallet | Exchange Wallet |
|---|---|---|---|
| Private Key Control | User-only, stored offline | Stored on device memory | Controlled by exchange |
| Login Verification | Physical device confirmation | Password or biometrics | Username & password |
| Hacking Risk | Extremely low | Medium | High |
| Recovery Options | Seed phrase backup | Cloud or local backup | Exchange-managed recovery |
Security Features of Trezor Login
- PIN Protection: Blocks unauthorized access attempts.
- Passphrase Option: Adds an extra security layer for hidden wallets.
- Firmware Verification: Prevents tampering by verifying authenticity.
- On-Device Confirmation: Every login or transaction must be physically approved.
- Recovery Seed: A 12- or 24-word phrase that restores your wallet if the device is lost.
Frequently Asked Questions (FAQs)
Q1: Can I log in to my Trezor wallet without the device?
No. Physical access to the Trezor device is mandatory for login. This ensures that no remote attacker can gain access to your wallet.
No. Physical access to the Trezor device is mandatory for login. This ensures that no remote attacker can gain access to your wallet.
Q2: What if I forget my PIN?
You can reset your device using your recovery seed. However, this wipes the device completely, so store your seed phrase securely.
You can reset your device using your recovery seed. However, this wipes the device completely, so store your seed phrase securely.
Q3: How often should I update my Trezor firmware?
Check for updates in Trezor Suite regularly. Firmware updates fix bugs, enhance login stability, and add support for new assets.
Check for updates in Trezor Suite regularly. Firmware updates fix bugs, enhance login stability, and add support for new assets.
Q4: Can Trezor Login be used with MetaMask?
Yes. You can connect your Trezor device through MetaMask using Trezor Bridge, which allows hardware-based authentication on the Ethereum network.
Yes. You can connect your Trezor device through MetaMask using Trezor Bridge, which allows hardware-based authentication on the Ethereum network.
Pro Tips for Safe Trezor Logins
- Always verify that your login request matches the URL “suite.trezor.io”.
- Never share your recovery seed or passphrase with anyone.
- Keep your Trezor device disconnected when not in use.
- Use strong device labels and passphrases for extra wallet layers.
- Back up your seed on metal or offline storage — never on cloud services.
“In cryptocurrency, your login is your lifeline. A secure Trezor Login isn’t just an entry point — it’s a digital shield protecting your financial independence.”
— Crypto Security Journal
Conclusion: Why Trezor Login Matters
The Trezor Login process is more than just a gateway to your crypto wallet — it’s a model of digital self-sovereignty. In an era where cyber threats evolve daily, hardware-based authentication remains the gold standard for crypto protection. Every confirmation click on your Trezor device is a declaration that your crypto belongs solely to you.
By understanding how to properly use Trezor Login, you empower yourself to manage, store, and trade digital assets securely. Whether you're holding Bitcoin, Ethereum, or a diversified crypto portfolio, your Trezor ensures that your keys never leave your hands.
Protect your digital wealth. Respect your login process. And remember: security begins with awareness — and ends with your Trezor Login.
By understanding how to properly use Trezor Login, you empower yourself to manage, store, and trade digital assets securely. Whether you're holding Bitcoin, Ethereum, or a diversified crypto portfolio, your Trezor ensures that your keys never leave your hands.
Protect your digital wealth. Respect your login process. And remember: security begins with awareness — and ends with your Trezor Login.